When the calf is separated from the herd, it becomes vulnerable and an easy prey for the pack. IT based companies are forced to send employees home to work remotely because of the pandemic and it has left many IT herds vulnerable to the cybercrime pack. Is fear and hopelessness the only remaining option for these herds? No. With a solid ITAD strategy and services like Unduit, even with the herd scattered there is no need to fear.
Organizations looking to secure themselves from cybercrime dangers must not only have a strong firewall but also a complete and efficient ITAD strategy. Some of the important parts of a great ITAD strategy are:
- Central Control Body: A specific department should be dedicated to handle all cybersecurity risk and ITAD processes. They should also classify the types of data that should be available departmentally and for how long the data should be available for. Then GDPR guidelines should be used to erase the data from the individual databases to avoid any liability issues.
- Company Asset Register: A register of all devices that are owned by the company and devices being used to access data remotely by employees should be made, authenticated and centralized. This will make sure that if any breach is attempted or made then the source can be tracked.
- Single Secure Cloud: Pick only one cloud provider that has a secure access point to help your organization be centralized and efficient when it comes to employees working remotely. This will help you manage both security risks and data flow easily through one single platform.
- Sanitize Old Equipment: Once devices that have been used whether remotely or within the organization, sanitize them according to GDPR guidelines or US state specific guidelines.
- Maintenance: Devices and equipment must be remotely maintained and have regular security and software updates to keep malware and other liability issues at bay. Proper guidelines must be followed.
- General Security Plan: a data security plan and policy must be in place that everyone in the organization must follow as a basic company protocol.
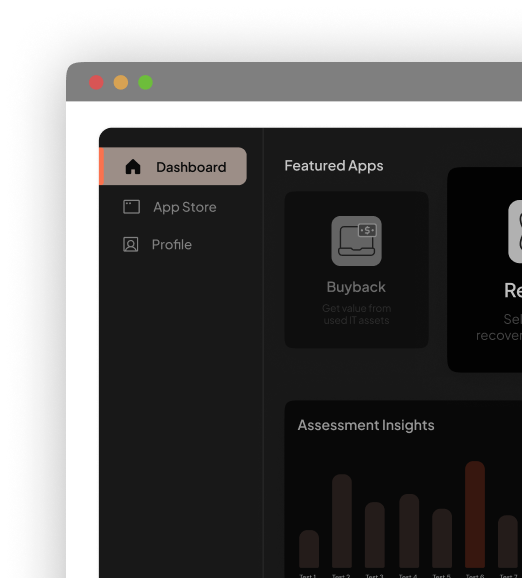
If these steps are followed correctly the herd is secure from predators waiting to feast but even the strongest of herds fall prey to them except those that are led by a shepherd. Unduit is one such shepherd that is leading the way in ITAD and is a one stop solution for all your organization’s mobility needs. Unduit can retrieve, aggregate, and responsibly dispose of assets from various users and reduce downtime drastically to improve device availability. All devices being refreshed would be available in weeks rather than months. With the enormous ecosystem of apps in the unduit platform all your ITAD issues can be addressed from a single source without having the need to search for multiple vendors. Unduit will do it all.